In today's digital landscape, WebSSH has emerged as a vital tool for secure remote access to servers and devices. It provides users with an efficient way to manage systems directly through web browsers, eliminating the need for additional software installations. WebSSH bridges the gap between traditional SSH clients and modern web-based interfaces, making it more accessible for both professionals and casual users alike.
As technology continues to evolve, the demand for flexible and secure methods of system administration grows exponentially. WebSSH not only fulfills this need but also enhances productivity by allowing administrators to perform tasks remotely without compromising on security. In this article, we will explore the various aspects of WebSSH, its advantages, potential use cases, and how it aligns with modern cybersecurity standards.
This guide is designed to provide a detailed understanding of WebSSH, catering to both beginners and advanced users. Whether you're a system administrator looking to streamline your workflow or a developer seeking secure remote access solutions, this article will equip you with the knowledge and tools necessary to harness the full potential of WebSSH.
What is WebSSH?
WebSSH is a web-based interface that allows users to establish secure shell (SSH) connections directly through their web browsers. This technology eliminates the need for dedicated SSH clients, making it an ideal solution for environments where installing additional software is not feasible. WebSSH leverages modern web technologies such as WebSockets and JavaScript to create a seamless user experience.
At its core, WebSSH provides a browser-based terminal emulator that communicates with remote servers via SSH protocols. This ensures that data transmitted between the client and server remains encrypted and secure, adhering to industry-standard encryption methods.
Key Features of WebSSH
- Browser-based interface for easy access
- Supports SSH protocols for secure connections
- Eliminates the need for additional software installations
- Compatible with modern web browsers
Benefits of Using WebSSH
WebSSH offers several advantages over traditional SSH clients, making it a preferred choice for many organizations and individuals. Below are some of the key benefits:
1. Enhanced Accessibility
With WebSSH, users can access their servers from any device with a web browser, eliminating the need for specific client applications. This flexibility is particularly beneficial for remote work scenarios or when working from devices with limited software capabilities.
2. Improved Security
WebSSH employs robust encryption methods to ensure secure communication between the client and server. By adhering to SSH protocols, WebSSH protects sensitive data from unauthorized access and potential cyber threats.
3. Cost-Effective Solution
Since WebSSH does not require additional software installations, it reduces the overall cost of managing remote servers. This makes it an attractive option for small businesses and individuals looking to optimize their resources.
Understanding WebSSH Architecture
The architecture of WebSSH involves multiple components working together to facilitate secure remote access. At a high level, the system consists of a client-side interface, server-side components, and the underlying SSH protocol.
Client-Side Components: The client-side interface is built using web technologies such as HTML, CSS, and JavaScript. It provides users with a terminal-like environment to interact with remote servers.
Server-Side Components: The server-side components handle the actual SSH connections and data transmission. These components often include WebSockets for real-time communication and SSH libraries for secure protocol implementation.
How WebSSH Works
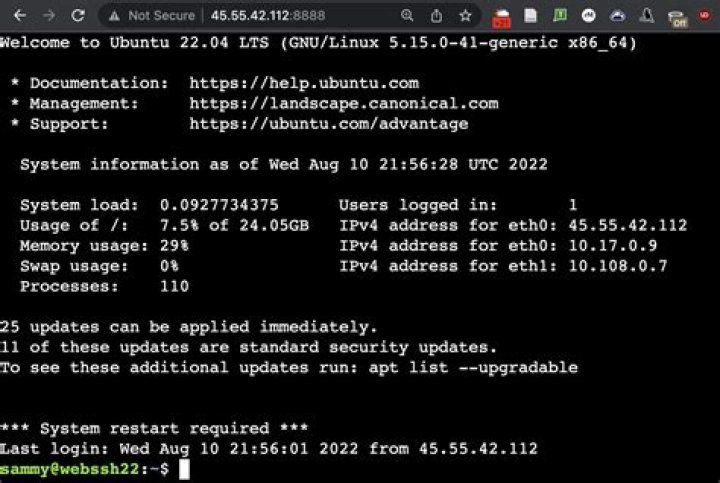
- User accesses the WebSSH interface through a web browser
- WebSSH establishes a WebSocket connection to the server
- SSH protocol is used to secure the communication channel
- User interacts with the remote server through the browser-based terminal
Security Features of WebSSH
Security is a critical aspect of WebSSH, as it deals with sensitive data and system access. Below are some of the key security features that make WebSSH a reliable solution:
1. Encryption
WebSSH employs industry-standard encryption methods to protect data in transit. This ensures that all communication between the client and server remains secure and tamper-proof.
2. Authentication
WebSSH supports various authentication methods, including username/password, SSH keys, and multi-factor authentication (MFA). These mechanisms provide an additional layer of security, preventing unauthorized access to remote systems.
3. Access Control
WebSSH allows administrators to define granular access controls, ensuring that users only have access to the resources they need. This helps maintain a secure environment by minimizing potential vulnerabilities.
Popular WebSSH Tools and Platforms
Several tools and platforms offer WebSSH functionality, each with its own unique features and capabilities. Below are some of the most popular options:
1. WebTerm
WebTerm is a lightweight WebSSH client that provides a simple and intuitive interface for remote server access. It supports SSH keys and offers basic terminal functionality, making it suitable for casual users.
2. AjaxTerm
AjaxTerm is another popular WebSSH tool that focuses on simplicity and ease of use. It allows users to access remote servers through a web browser without requiring additional software installations.
3. Shellinabox
Shellinabox is a more advanced WebSSH solution that offers enhanced features such as file transfer and multi-user support. It is ideal for organizations requiring more sophisticated remote access capabilities.
How to Set Up WebSSH
Setting up WebSSH involves several steps, depending on the specific tool or platform being used. Below is a general guide to help you get started:
Step 1: Choose a WebSSH Tool
Select a WebSSH tool that aligns with your requirements and technical expertise. Popular options include WebTerm, AjaxTerm, and Shellinabox.
Step 2: Install the Tool
Follow the installation instructions provided by the chosen tool. This typically involves downloading the software and configuring it to work with your server environment.
Step 3: Configure SSH Settings
Set up the necessary SSH configurations, including authentication methods and access controls. Ensure that all security settings are properly configured to protect your system.
Step 4: Test the Connection
Once the setup is complete, test the WebSSH connection to ensure that it is functioning correctly. Verify that you can access your remote server through the web-based interface.
Real-World Use Cases of WebSSH
WebSSH finds applications in various industries and scenarios, where secure remote access is essential. Below are some real-world use cases:
1. Cloud Computing
Cloud service providers often use WebSSH to allow customers to manage their virtual machines and infrastructure directly through web browsers.
2. DevOps
DevOps teams leverage WebSSH for streamlined system administration tasks, such as deploying code, monitoring server performance, and troubleshooting issues.
3. Remote Work
With the rise of remote work, WebSSH has become a valuable tool for employees who need to access company servers from different locations without installing additional software.
Limitations and Challenges
While WebSSH offers numerous advantages, it also has certain limitations and challenges that users should be aware of:
1. Performance
WebSSH performance may vary depending on the quality of the internet connection and the capabilities of the web browser being used. This can impact the user experience, especially for resource-intensive tasks.
2. Browser Compatibility
Not all web browsers fully support the technologies required for WebSSH functionality. Users may encounter compatibility issues when using outdated or less common browsers.
3. Security Risks
Although WebSSH employs robust security measures, improper configurations or weak authentication methods can expose systems to potential vulnerabilities. It is crucial to follow best practices to minimize these risks.
WebSSH vs Traditional SSH Clients
When comparing WebSSH to traditional SSH clients, several factors come into play, including accessibility, security, and ease of use. Below is a comparison of the two approaches:
1. Accessibility
WebSSH offers greater accessibility, as it allows users to access servers from any device with a web browser. Traditional SSH clients, on the other hand, require specific software installations, limiting their usability.
2. Security
Both WebSSH and traditional SSH clients provide secure communication channels using SSH protocols. However, WebSSH may introduce additional security risks if not properly configured or used in conjunction with outdated browsers.
3. Ease of Use
WebSSH simplifies the user experience by eliminating the need for additional software installations. Traditional SSH clients, while more feature-rich, may require more technical expertise to set up and use effectively.
The Future of WebSSH
As technology continues to advance, the future of WebSSH looks promising. With the growing demand for flexible and secure remote access solutions, WebSSH is likely to become even more prevalent in various industries.
Future developments may include improved performance, enhanced security features, and better browser compatibility. Additionally, the integration of WebSSH with emerging technologies such as artificial intelligence and machine learning could further enhance its capabilities and usability.
Conclusion
WebSSH has revolutionized the way users interact with remote servers, providing a secure and accessible solution for system administration tasks. By leveraging modern web technologies and adhering to industry-standard security protocols, WebSSH offers a reliable alternative to traditional SSH clients.
In this article, we explored the various aspects of WebSSH, including its architecture, benefits, security features, and real-world use cases. We also discussed its limitations and compared it to traditional SSH clients, highlighting the key differences and considerations.
As you embark on your journey with WebSSH, we encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into the world of cybersecurity and technology.